Microsoft Entra ID
In this guide, you’ll learn how to set up Microsoft Entra ID in Coalesce.
You must be a Microsoft Entra ID Administrator to complete this process.
Before You Begin
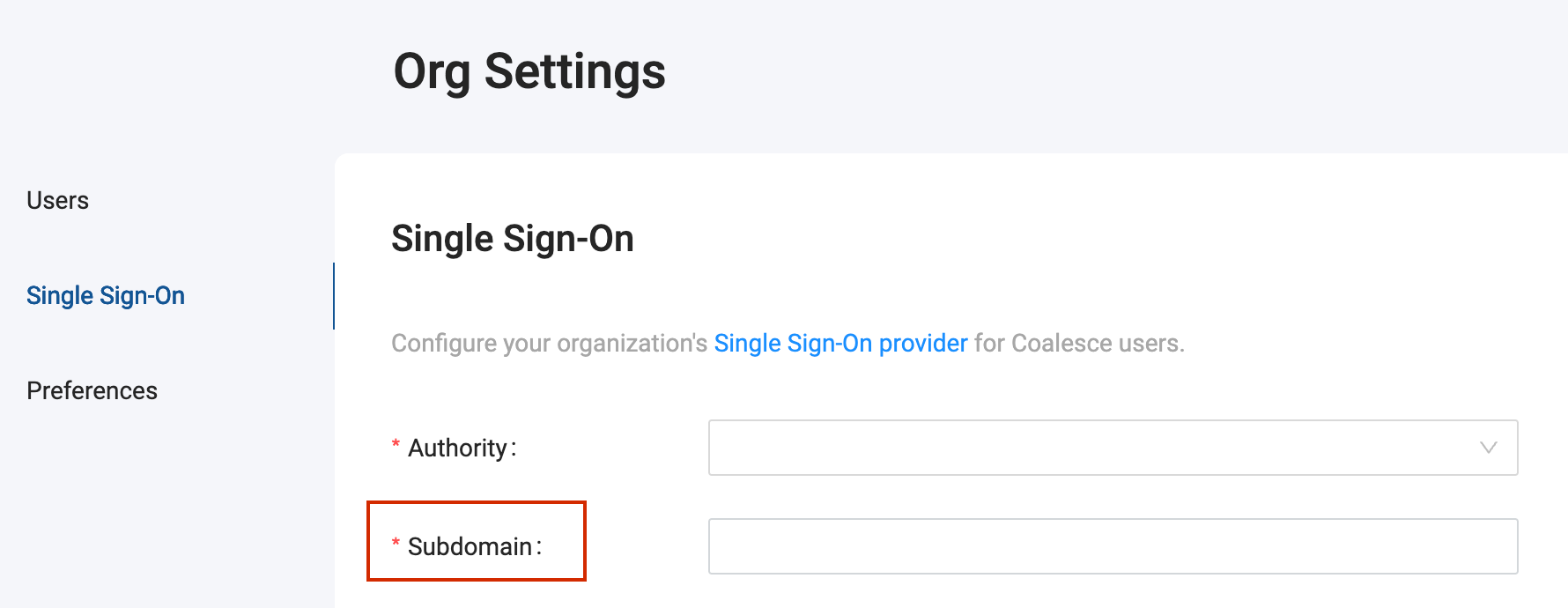
Get Your Subdomain
Your subdomain is the subdomain of your Coalesce instance. For example, if you login at https://testapp.app.coalescesoftware.io/. Your subdomain is testapp.
To check if already have a subdomain, go your organizations single sign-on settings.
If you don't have a subdomain, you can add one to the subdomain box. Coalesce will automatically configure your subdomain based on the name entered. Check with your IT team before adding it to your organizations settings.
Microsoft Entra ID Permissions
When selecting Use Single-Sign On with Microsoft Entra ID, you may be prompted to grant Coalesce permission to:
- Sign you in and read your profile
- Maintain access to data you have given it access to
- Microsoft Graph:
emailprofileUser.Readopenid
These permissions can be pre-approved for future users by an admin in Microsoft Entra ID.
- Go to Manage > App Registrations > Your App Registration > API Permissions.
- Then select Add a permission > Microsoft Graph > Delegated Permissions and then select the desired permissions to pre-approve for the non-admin users.
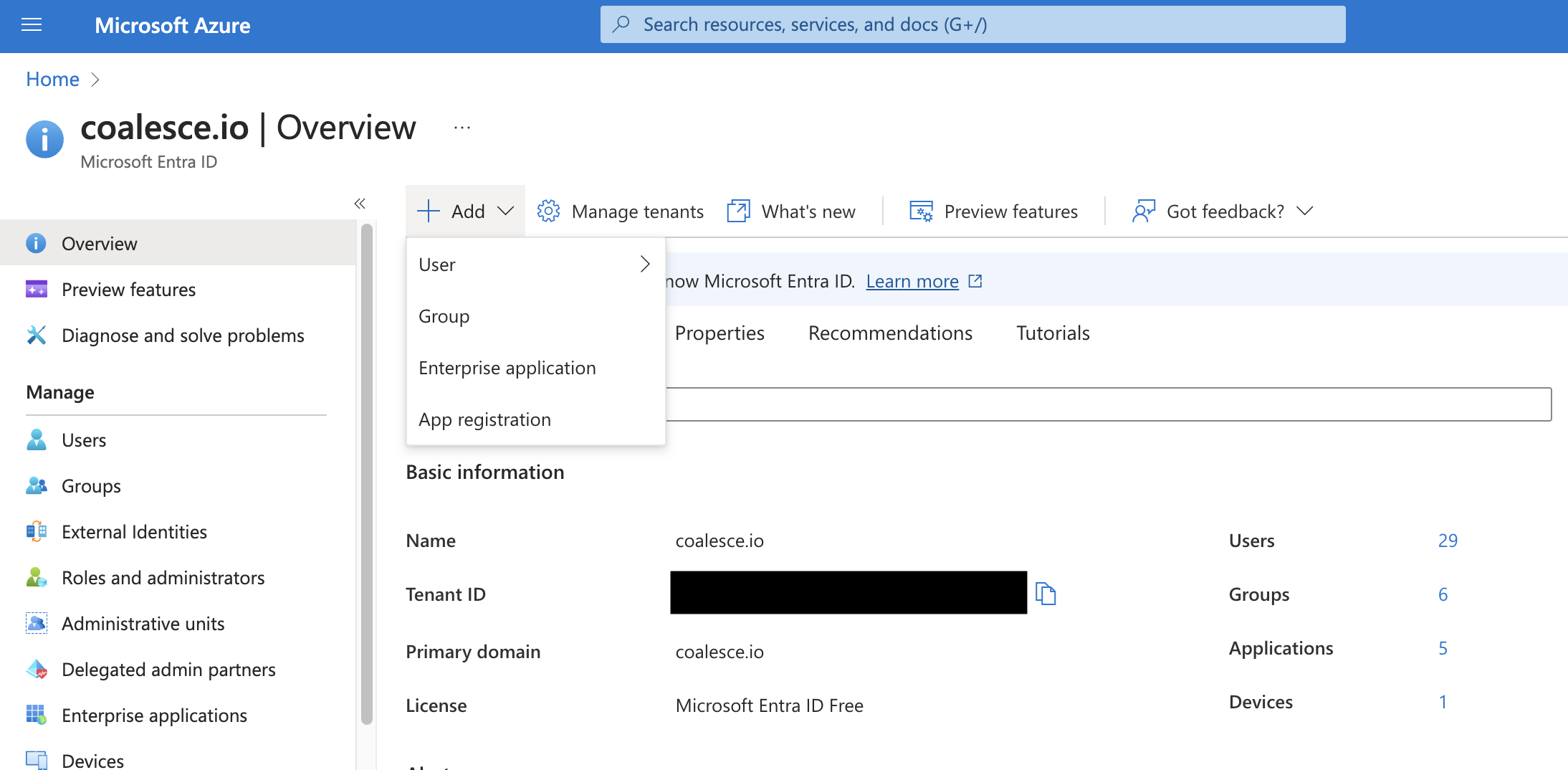
Configure Microsoft Entra ID
To use Microsoft Entra ID as your Single Sign-On provider, you'll want to create a new App Registration in Azure.
-
Go to the Overview panel in Azure Active Directory
-
Click the +Add dropdown
-
Select App Registration
-
On the registration page for this newly created integration, enter the following:
- Name - this is typically going to be
Coalescebut any friendly name works - Supported Account Types - choose which Account types to support, see the following screenshot.
- Make sure you choose Single Page Application (SPA).
- Redirect URI - The redirect URI should be formatted as follows -
https://mySubdomain.<app_domain>/login/callback.- Create a subdomain if one hasn’t already been defined for your organization. We recommend choosing a name specific to your organization. If the Subdomain box in your Single Sign-On Settings is blank, you can create one by adding it in the subdomain box.
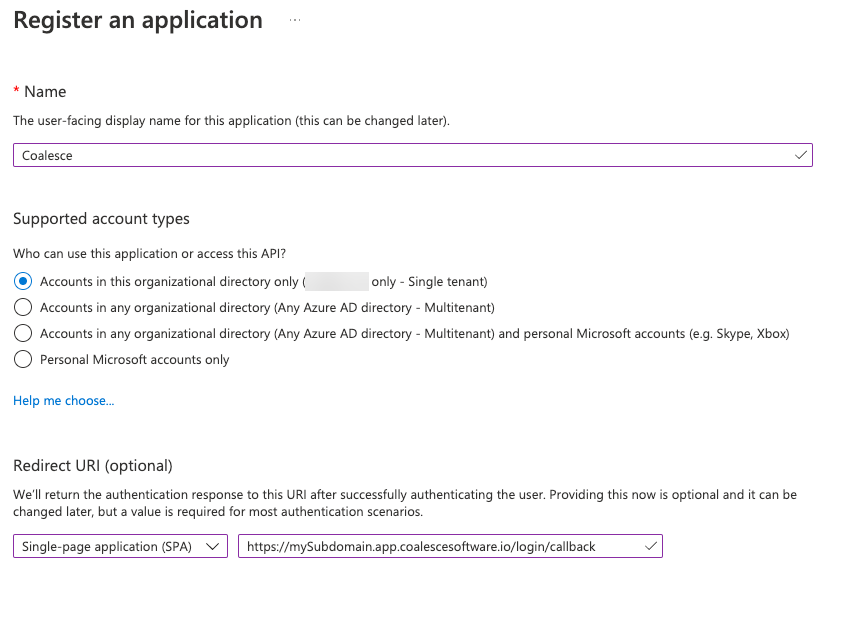 Supported Account Types
Supported Account TypesPersonal Microsoft accounts only is not a supported option for Coalesce Microsoft Entra ID SSO.
- Name - this is typically going to be
-
Click Register to create the integration. You'll now be at a window with all your App Registration settings.
-
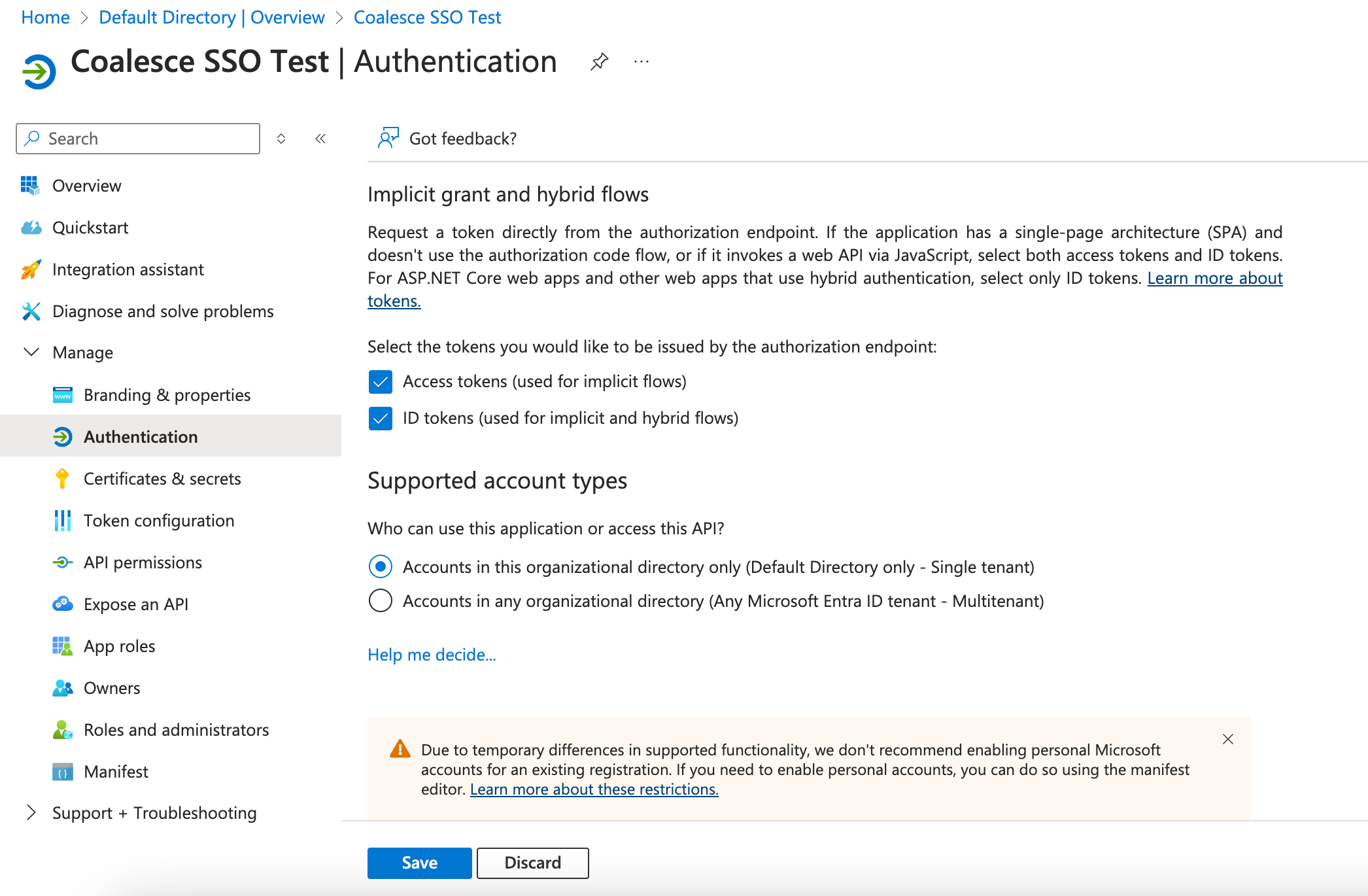
While still in Azure, go to Manage > Authentication.
-
Scroll down to Implicit grant and hybrid flows. Select both: Access tokens (used for implicit flows) and ID tokens (used for implicit and hybrid flows) and Save.
-
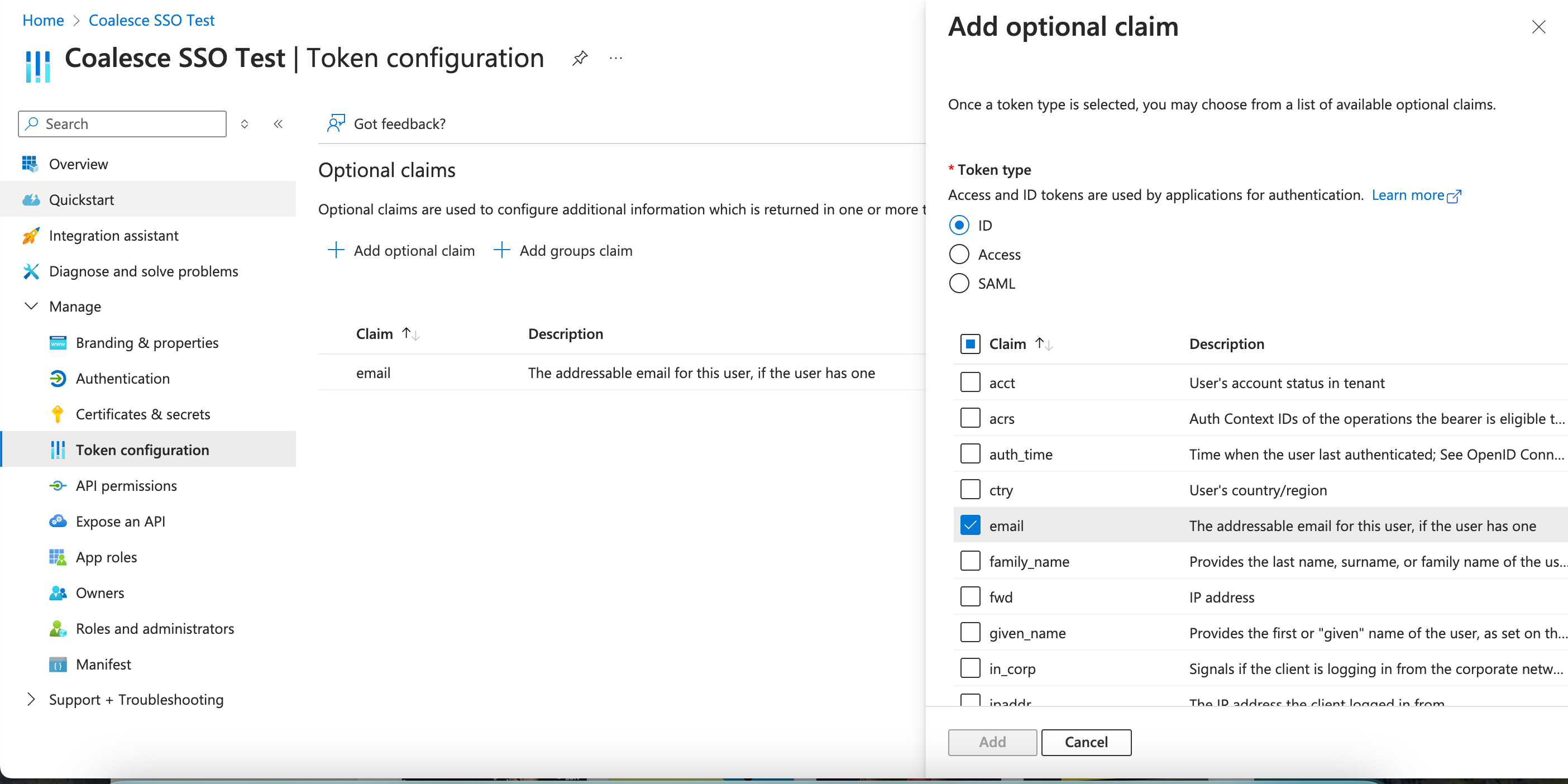
Go to Manage > Token configuration.
-
Click Add optional claim.
-
Choose ID as the Token Type.
-
Select email and Save.
-
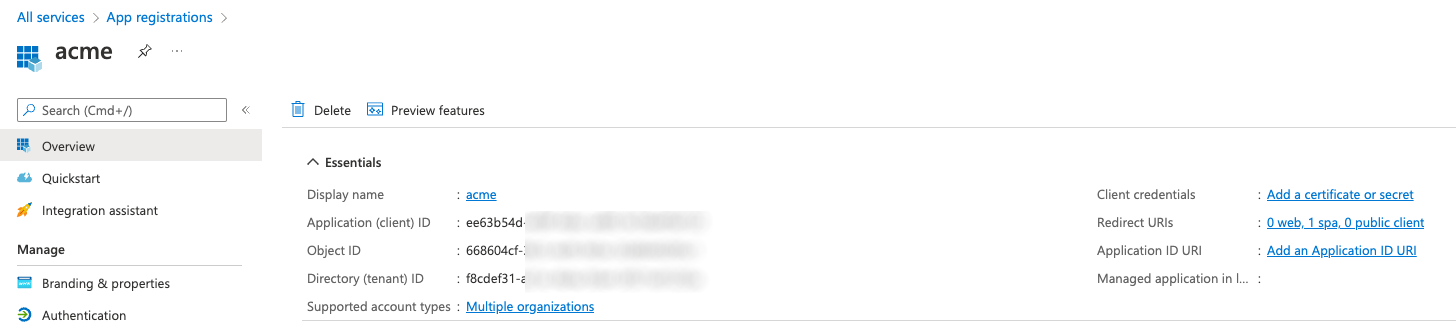
Go back to the Overview. You'll need the information to finish configuration in Coalesce.
Configure Coalesce Microsoft Entra ID Settings
-
Open a new window.
-
Sign in to your Coalesce application using username and password.
-
Go to Organization Settings > Single Sign-On.
-
Enter in the following information:
Field Description Authority The system being used for Single Sign On. Choose Azure. Subdomain This will be the same as mySubdomain. Not the entire redirect URI.Authorization Server Single for tenant integrations. https://login.microsoftonline.com/[tenantID]/Authorization Server for multi-tenant and multi- personal integrations https://login.microsoftonline.com/common/OIDC Client ID Refer to the Application (client) ID in the "Essentials" section on the overview page for your App Registration. Server-Side Authorization (Optional) Toggle on to add an authorization URL. Use this when the authorization server blocks access to the OpenID configuration or token endpoints. Authorization Endpoint (Available with Server-Side Authorization ) The authorization URL to redirect to. 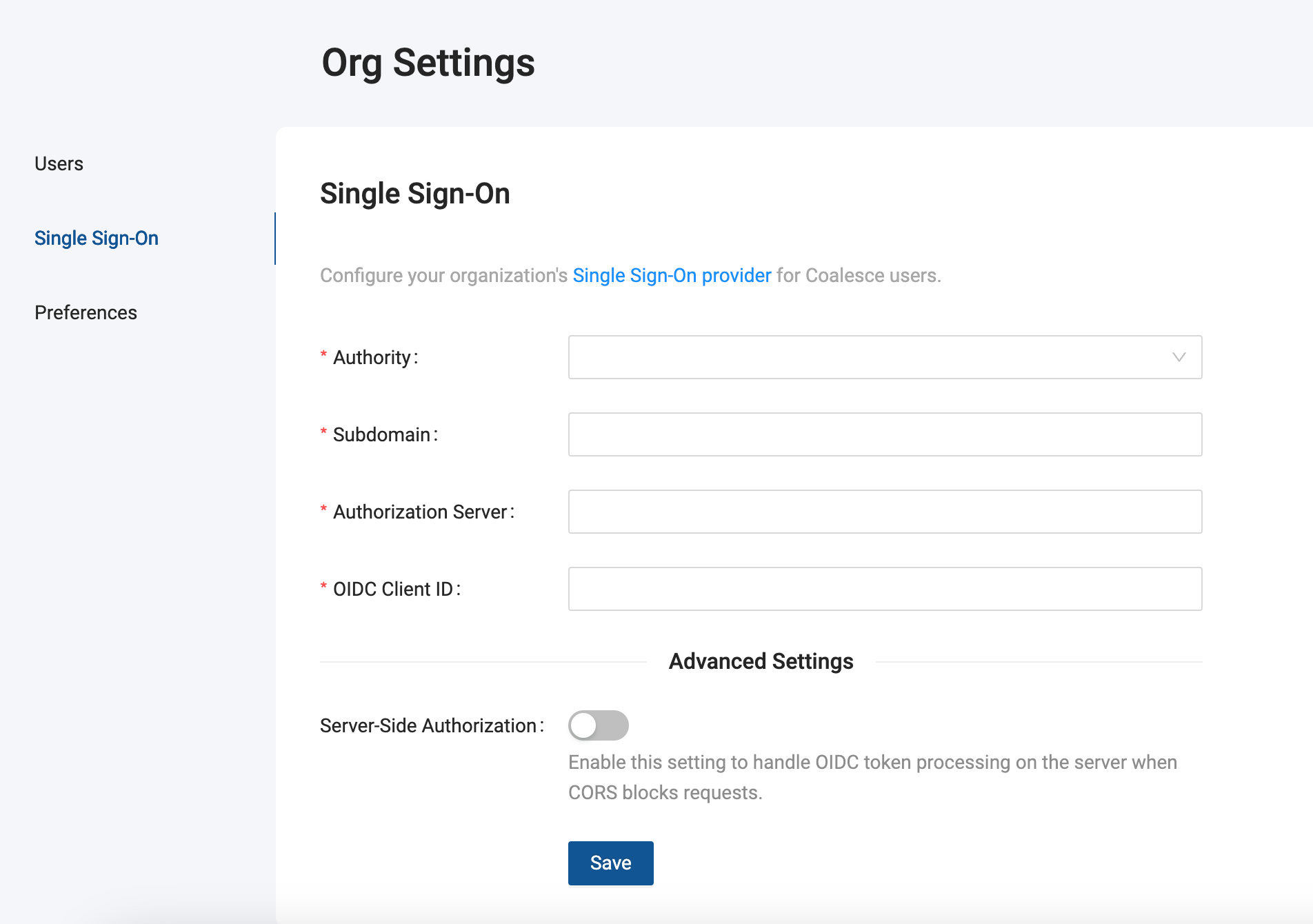
-
Once you've filled out the SSO settings in Coalesce, click Save.
-
Log out of Coalesce.
-
Go to your SSO URL, which will be formatted like -
https://mySubdomain.<app_domain>- and click on the Use Single Sign-On button to log in using SSO.
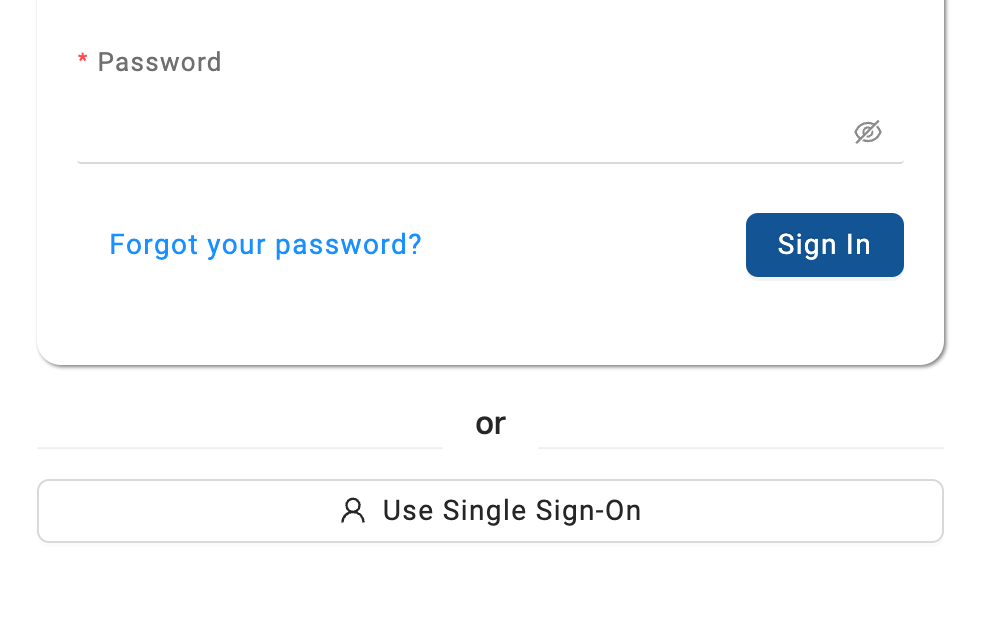
If instead of a button you see an error message, check to make sure you correctly entered all the fields in your Coalesce SSO settings. If the problem persists please reach out to our Support Team.
Duplicate Accounts After SSO Setup
The creation of a separate SSO account is expected behavior and does not affect your existing basic auth account's permissions.
When you first authenticate using SSO in Coalesce, the system creates a new SSO account separate from your existing basic authentication account. This new SSO account is automatically assigned Org Member permissions by default.
If you previously had admin permissions through your basic auth account, you'll need to update the permissions for your new SSO account. To do this:
- Log in using your basic authentication credentials.
- Update the permissions for your SSO account.
- If you don't have admin access, contact your organization's admin to update the permissions.